Integrating Cisco Virtual Internet Routing Lab (VIRL) with Nectus
In this article we will see some of the features of Nectus that can enhance the Virtual Internet Routing Lab (VIRL) experience.
VIRL is Cisco’s network simulation platform where you can run Cisco OS (IOS, IOS XE, IOS XR, NX-OS, ASA) virtual machines and other third party virtual machines (this includes Linux servers, traffic generators and other networking vendors virtual machines) to build topologies for feature testing and validation before introducing them in production.
We will explain some features of Nectus that can complement VIRL to help you visualize better your network.
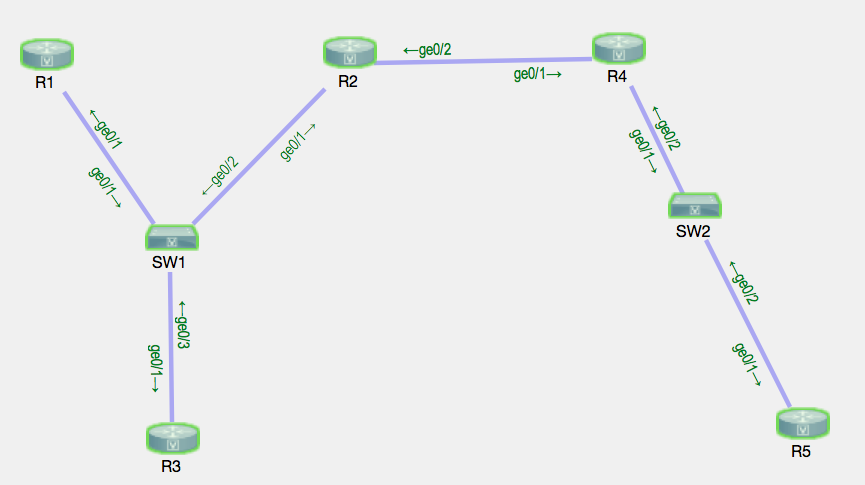
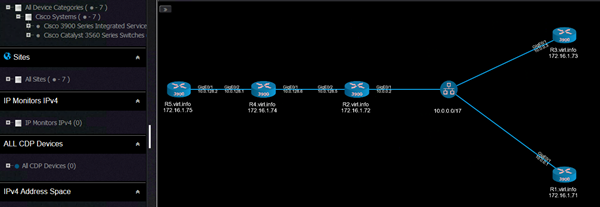
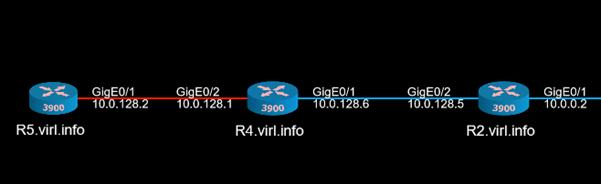
This is the VIRL topology that will be used:
The devices were started with some predefined configuration that included interface IP configuration, routing protocols (EIGRP, BGP).
VIRL topology is using shared flat network so that each device will get an IP address from 172.16.1.0/24 network on their GigabitEthernet0/0 interface as their management IP address.
Nectus was installed on a Windows 2016 server that was acting as an OpenVPN client connecting to VIRL server which means that it received an IP address from the range 172.16.1.20 – 172.16.1.39, thus making the Nectus and the VIRL routers to be in the same subnet.
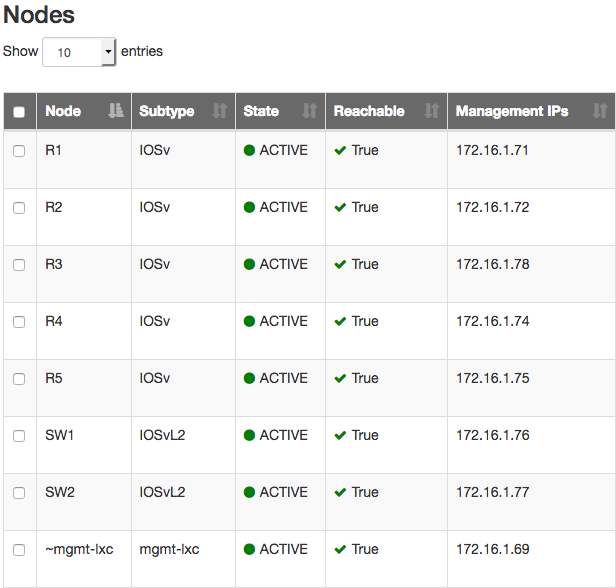
Once Nectus starts discovering the devices from 172.16.1.0/24 subnet (as per discoverable subnets configured on Nectus), it builds a list with them categorizing them based on the vendor, type of the device, model of the device.
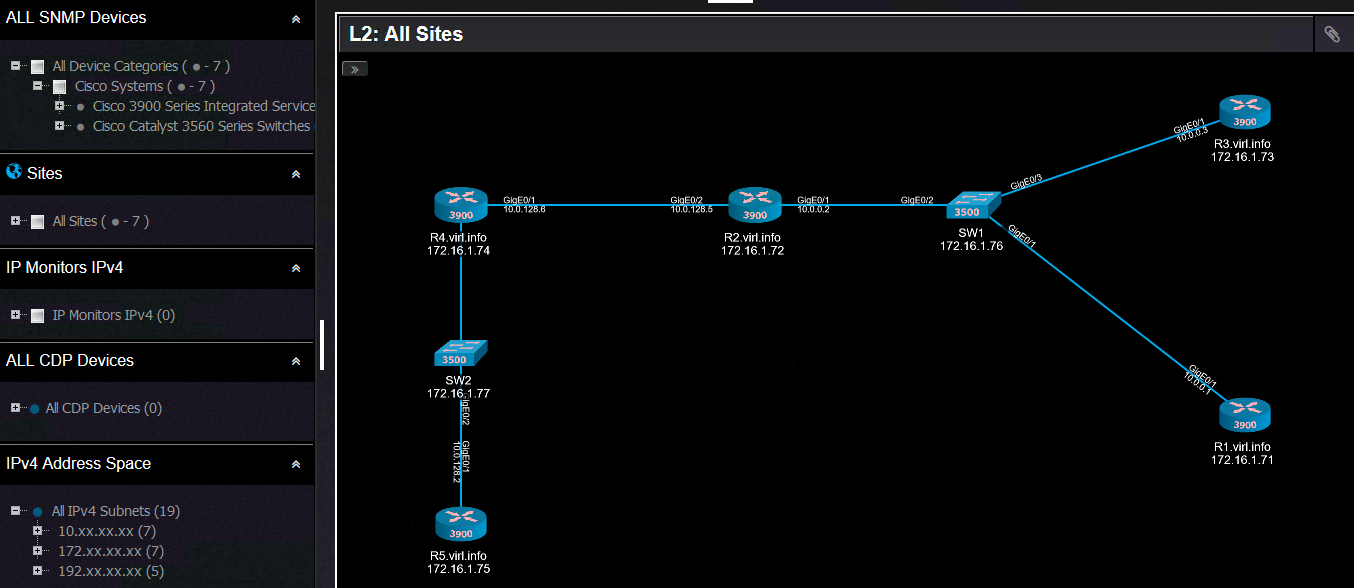
Based on the information collected through SNMP, Nectus can build L2 and L3 topologies.
This is the L2 topology:
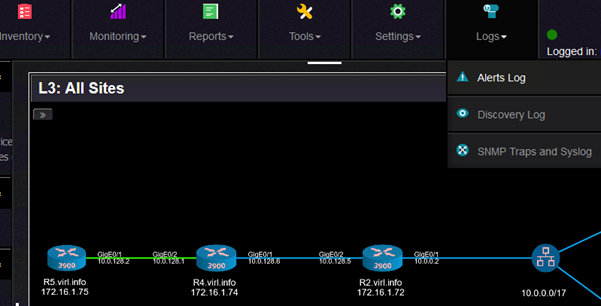
And this is the L3 topology:
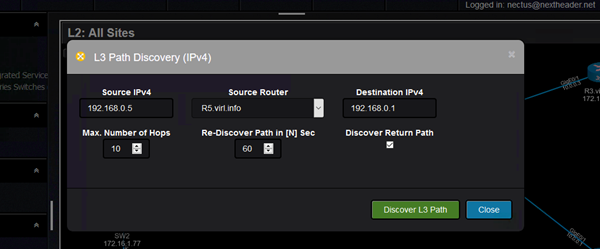
One interesting feature that Nectus can do is to give you a visual result of the path between two points in the network.
This is called L3 Path Discovery (for now only available for IPv4). Source IP, source router and destination IP are the input values:
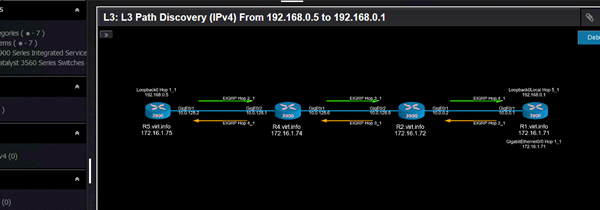
And the result looks like this:
The interesting part is that it can discover asymmetric paths in the network to give a better understanding about how traffic flows in the network.
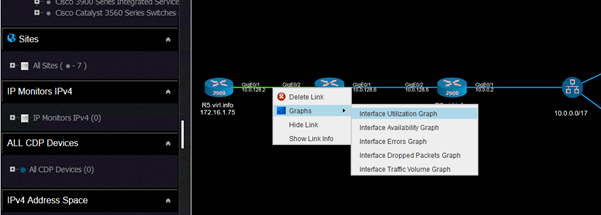
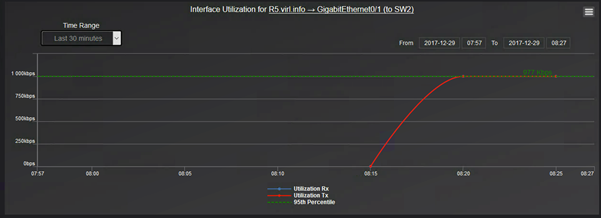
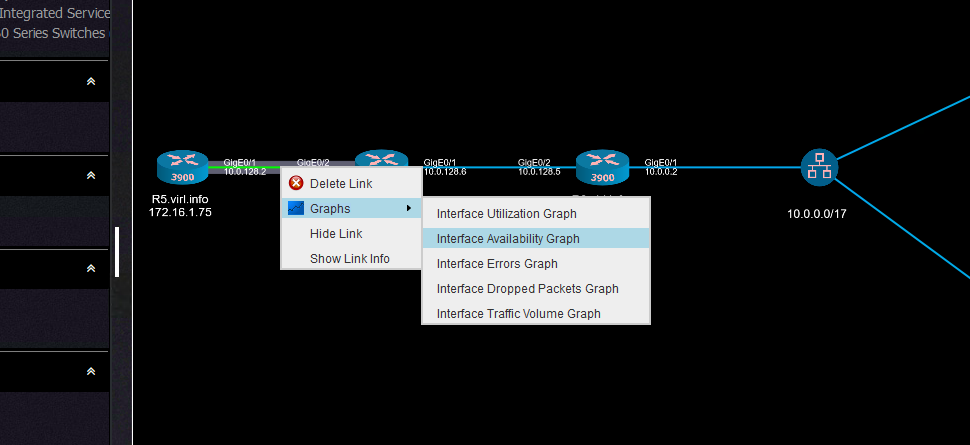
Another interesting set of features is that you can get real time graphs with the some of the characteristics of the interfaces (utilization, availability, errors, dropped packets, traffic volume).
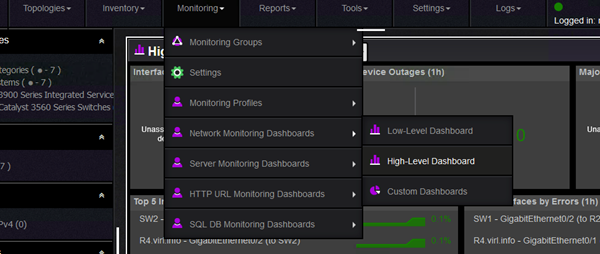
This is how you can select any of the graphs. This is for utilization:
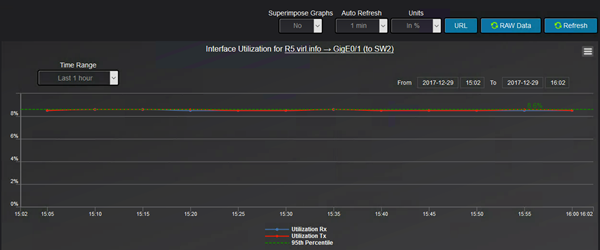
And the graph looks like this:
Observe that although on when we selected the link that appear to be between R5 and R4, it is actually between R5 and SW2.
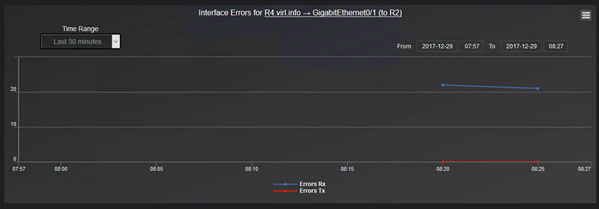
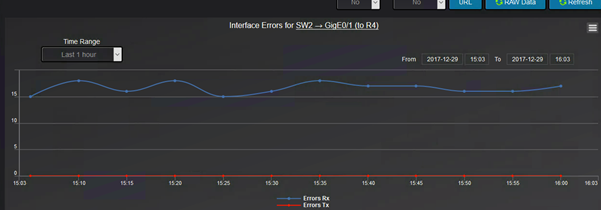
The errors graph shows how many RX and how many TX errors are on interface basis:
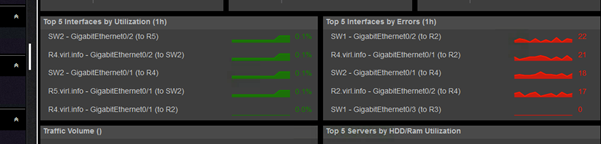
You can have a consolidated view of the top most utilized interfaces or the interfaces that have the most errors.
By default, there are few network monitoring dashboards (you can create your own to better accommodate your monitoring needs).
The high level dashboard gives you the top interfaces with regards to various interface statistics:
From here, you will get the the list of interfaces:
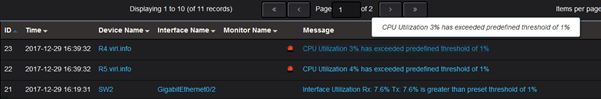
Nectus can trigger alerts based on any of these interface characteristics.
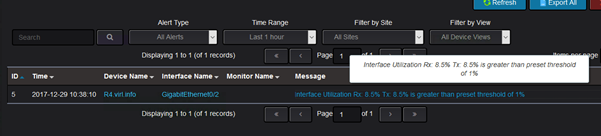
For testing purposes, the threshold level for interface utilization at which the alarm is triggered was configured at 1%.
Using ping command (between R4 and R5, therefore through SW2), the interface utilization was around 870Kbps and after changing the bandwidth of the interface to 10Mbps
(adding bandwidth knob under interface configuration), this 870Kbps turned out to be around 8.5% interface utilization which means that the alert should have been triggered.
After some time, the graph is adjusted with the new value:
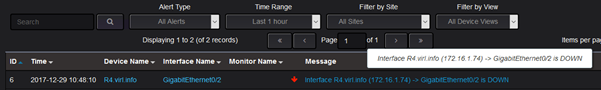
The alerts log shows these type of alerts:
And in this interface utilization, this is the alert:
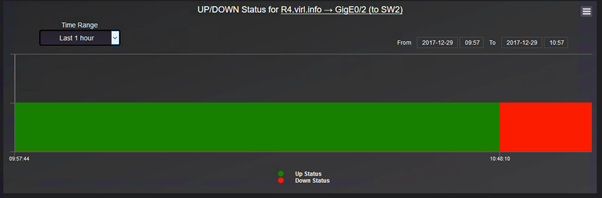
Another useful information that can be retrieved directly from Nectus using the interface graphs is the interface availability that can quickly give some hints about service interruption.
The graph is selected from the link menu:
And it should show the state of the interface:
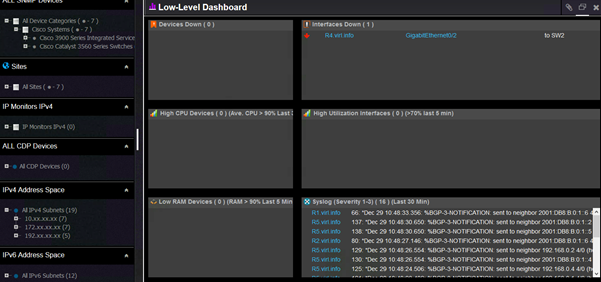
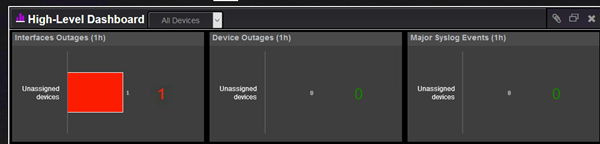
Coming back to the default network monitoring dashboards, the information that an interface that is down is captured by both default dashboards. This is the low level dashboard:
As well by the high level dashboard:
Again, there is an alert sent for such events:
There is a history kept for each outage of the interfaces showing for how long the interface was down:
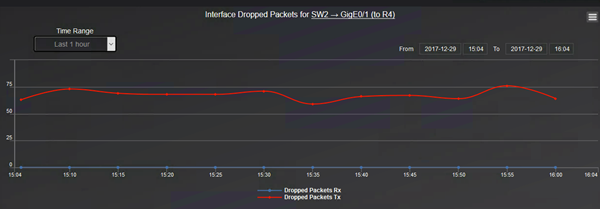
Going further graphs for interface errors and dropped packets are useful to troubleshoot network performance.
And for dropped packets:
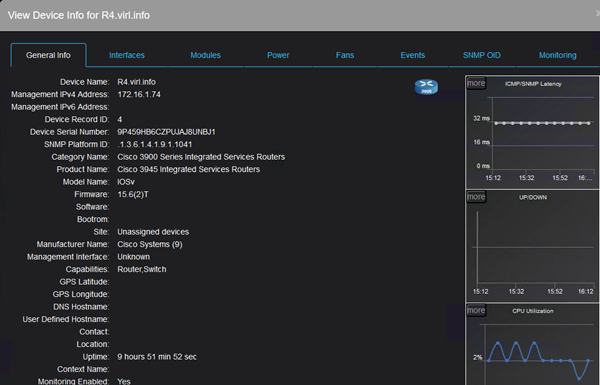
Coming back to alerts, Nectus can monitor the CPU usage and trigger alerts as required.
The Device Info menu contains among other CPU usage graphs.
If the CPU usage goes above the threshold, not only you will see this on the graph, but it will also trigger an alert:
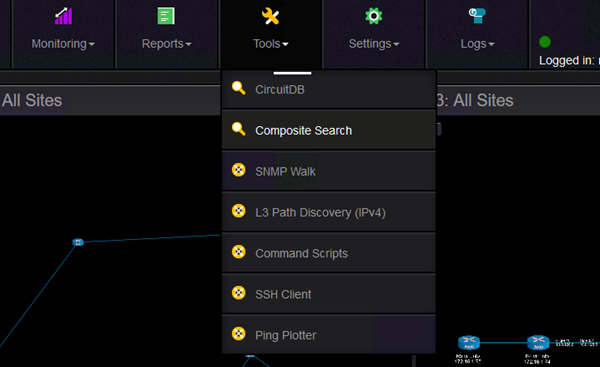
Another interesting feature that can help you quickly find all sort of information about the devices in your topology is the Composite Search feature:
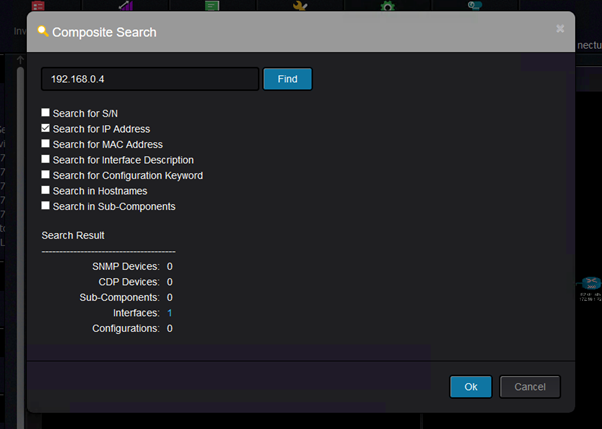
It can find various information and for instance, I would like to find where is this IP configured:
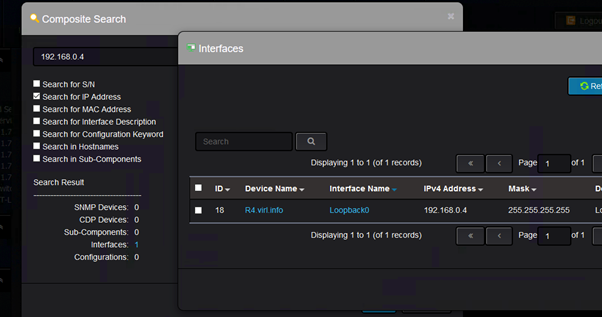
And the result is this:
Lastly, one feature that can improve VIRL usability is that Nectus can show on the topology that a link is down
(after the link was shutdown from CLI or went down for other reasons like err-disable).
Suppose you do this on CLI:
R4(config)#int gi0/2
R4(config-if)#shut
R4(config-if)#
*Dec 29 17:35:29.750: %DUAL-5-NBRCHANGE: EIGRP-IPv6 1: Neighbor FE80::F816:3EFF:FE84:2418 (GigabitEthernet0/2) is down: interface down
*Dec 29 17:35:29.752: %DUAL-5-NBRCHANGE: EIGRP-IPv4 1: Neighbor 10.0.128.2 (GigabitEthernet0/2) is down: interface down
*Dec 29 17:35:31.725: %LINK-5-CHANGED: Interface GigabitEthernet0/2, changed state to administratively down
*Dec 29 17:35:32.725: %LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/2, changed state to down
R4(config-if)#
Then the link will blink on the topology, while VIRL will not show anything with regards to the fact that the interface between the VMs is down:
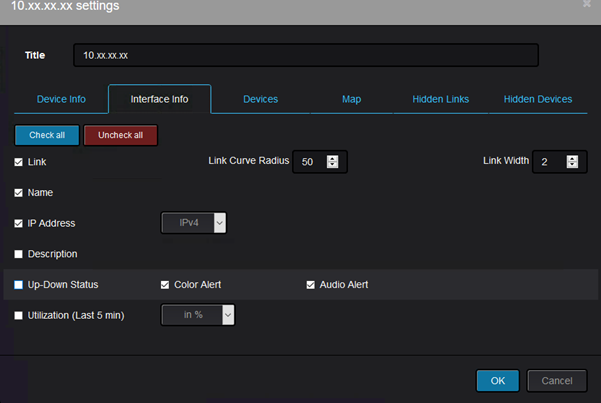
The up/down status can be enabled from the device settings like this:
Throughout this post, various features of Nectus have shown how Nectus5 can bring value to topologies running in Cisco VIRL.
Of course the same features can be used to know your real/production network better, but it is good to know that you can use Nectus5
to monitor your proof of concept network deployed in VIRL.

Leave a Reply
Want to join the discussion?Feel free to contribute!